Cryptocurrencies are often described as digital money, but unlike traditional money, they do not sit in a bank account or a physical wallet. Instead, they exist on a blockchain, a public digital ledger. To access and manage these assets, users need a crypto wallet. Understanding how crypto wallets work is one of the most important steps for anyone entering the world of digital assets. A crypto wallet is not a place where coins are stored in the usual sense. Rather, it is a tool that allows you to interact with the blockchain. It helps you send, receive, and manage cryptocurrencies securely. Without a wallet, you cannot truly own or control your crypto.
- What is a Crypto Wallet?
- How Crypto Wallets Work
- Why Crypto Wallets Matter
- Types of Crypto Wallets
- Custodial vs Non Custodial Wallets
- Common Features of Crypto Wallets
- Choosing the Right Crypto Wallet
- Popular Types of Crypto Wallets in Practice
- Wallet Security Best Practices
- Common Wallet Mistakes to Avoid
- The Role of Wallets in the Crypto Ecosystem
- Final Thoughts
- FAQ
This guide explains what a crypto wallet is, how it works, and why it matters. It also introduces the major types of wallets, their features, and the key differences every beginner should understand before choosing one.
What is a Crypto Wallet?
A crypto wallet is a software application or physical device that stores the cryptographic keys required to access and control your cryptocurrency. These keys are what prove ownership on the blockchain.
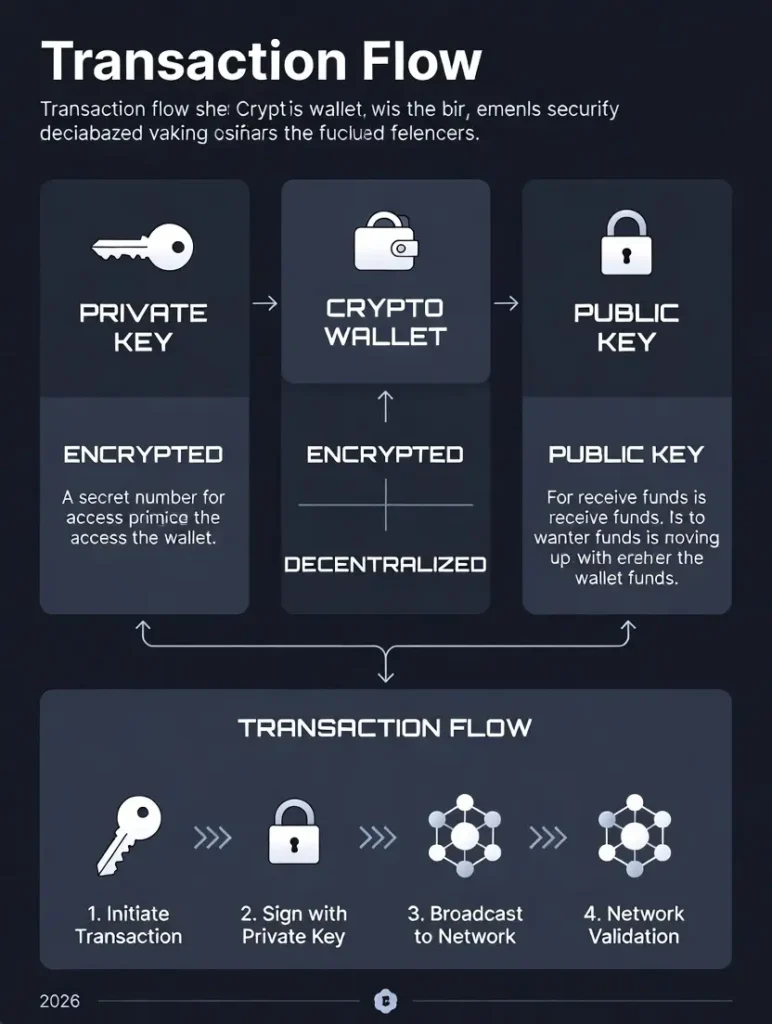
There are two types of keys involved. A public key acts like an address. You can share it with others to receive funds. A private key is like a password. It gives full control over the crypto associated with that address. Anyone who has access to the private key can move the funds.
The wallet’s primary role is to store and manage these keys safely. When you send crypto, the wallet signs the transaction using your private key and broadcasts it to the blockchain network. When you receive crypto, the wallet shows your updated balance by reading blockchain data.

This is why security is so critical. Losing your private keys usually means losing access to your funds permanently.
How Crypto Wallets Work
To understand crypto wallets, it helps to separate ownership from storage. Cryptocurrencies never leave the blockchain. What changes is who has the authority to control them. When you create a wallet, it generates a set of cryptographic keys. The public key becomes your wallet address. The private key remains secret and is used to authorize transactions.
Most modern wallets also generate a recovery phrase, often called a seed phrase. This is a series of 12 or 24 words that can recreate your wallet and private keys. If your device is lost or damaged, this phrase is the only way to recover your funds.
When you make a transaction, the wallet does the following:
- Creates a transaction request
- Signs it is using your private key
- Sends it to the blockchain network
- Waits for confirmation from the network
At no point does the wallet hold actual coins. It simply proves that you have the right to move them.
Why Crypto Wallets Matter
Crypto wallets are essential because they give users control. In traditional finance, banks hold your money and manage access. In crypto, the wallet puts that responsibility in your hands.
This has major benefits. You can send money globally without intermediaries. You can hold assets without relying on a central authority. You can interact with decentralized applications and financial services directly.
However, it also comes with responsibility. No customer support desk can reset your password if you lose your private key. Security and good wallet practices are not optional. They are part of ownership.
Types of Crypto Wallets
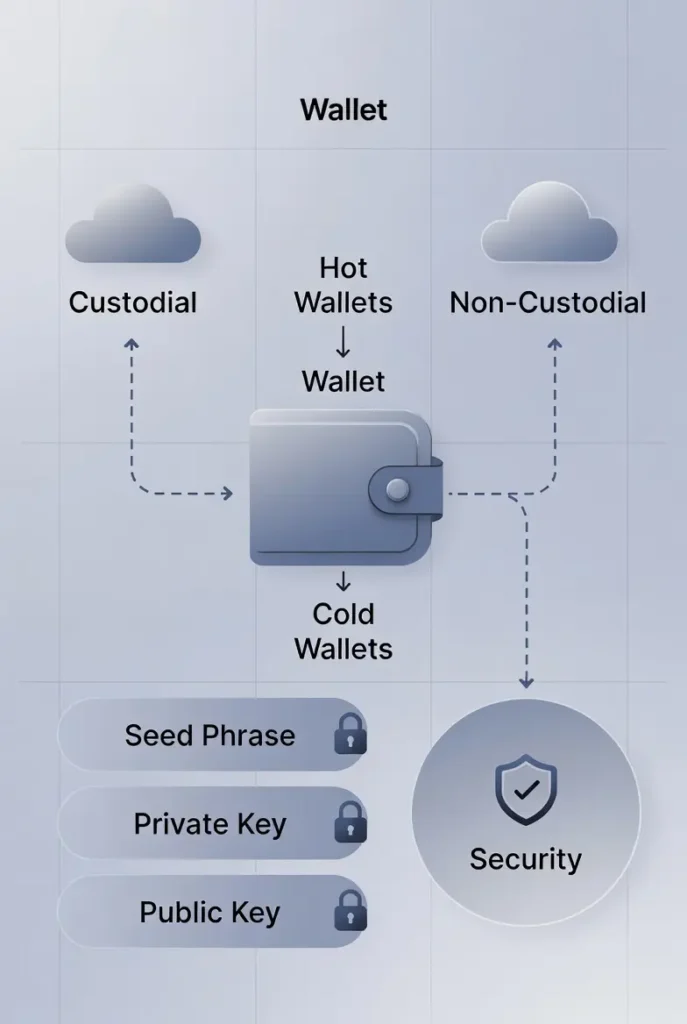
Crypto wallets are commonly classified in two main ways. The first is hot versus cold wallets. The second is custodial versus non-custodial wallets. Understanding both distinctions is crucial.

Hot Wallets
Hot wallets are connected to the internet. They are usually software-based and designed for convenience and frequent use. Examples include mobile wallets, desktop wallets, and web wallets. These wallets are easy to set up and user-friendly. They are often free and support multiple cryptocurrencies.
Hot wallets are ideal for daily transactions, trading, and interacting with decentralized applications. However, because they are online, they are more exposed to hacking risks. If your device is compromised, your wallet could be at risk. Crypto wallet security depends heavily on strong passwords, device protection, and safe storage of recovery phrases.
Cold Wallets
Cold wallets store private keys offline. They are designed for long-term storage and higher security.
The most common cold wallets are hardware wallets and paper wallets. Hardware wallets are physical devices that store keys in a secure chip. They connect to a computer or phone only when signing a transaction.
Because cold wallets are not constantly connected to the internet, they are far less vulnerable to online attacks. This makes them a popular choice for holding large amounts of cryptocurrency.
The trade-off is convenience. Cold wallets are slower to access and usually cost money to purchase.
| Feature | Hot Wallets (Online) | Cold Wallets (Offline) |
|---|---|---|
| Connection | Internet-connected | No internet (or air-gapped) |
| Convenience | High (quick trades, dApps) | Lower (manual connect needed) |
| Security | Medium (vulnerable to hacks/phishing) | High (immune to online attacks) |
| Best For | Daily use, small amounts | Long-term holding, large holdings |
| Examples | Mobile/desktop apps, browser extensions | Hardware devices, paper wallets |
| Cost | Usually free | $50–$200+ for hardware |
| Risk Level | Higher if device compromised | Lower, but risk of physical loss |
Visit this guide hot vs cold wallets differences
Custodial vs Non Custodial Wallets
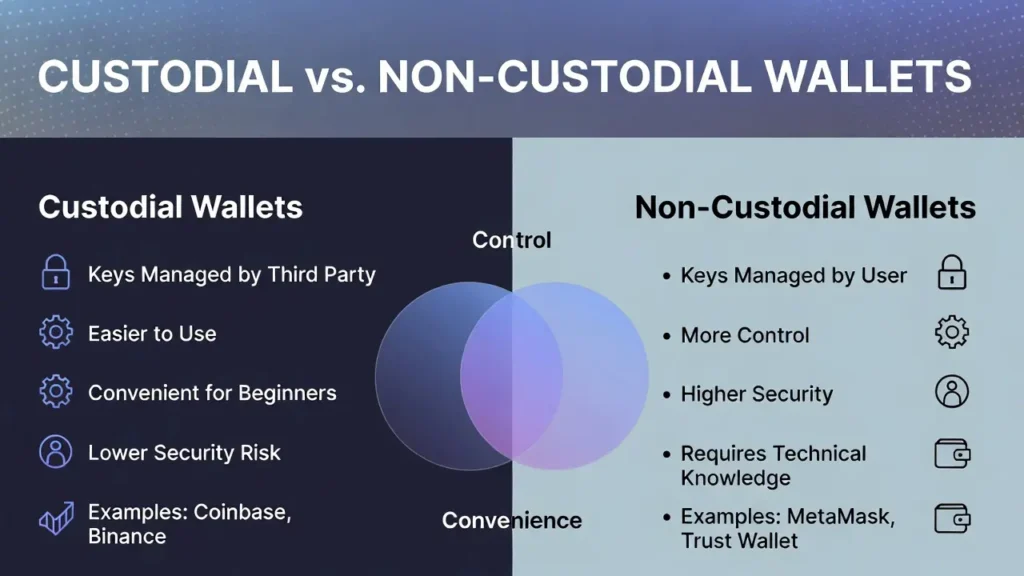
Another critical distinction is who controls the private keys.
Custodial Wallets
Custodial wallets are managed by a third party, usually an exchange or platform. The service provider holds your private keys on your behalf.
These wallets are easy to use and suitable for beginners. Password recovery and customer support are often available. If you forget your login details, the platform can help restore access.
However, you do not have full control over your funds. If the platform is hacked, frozen, or shut down, your assets may be at risk. This goes against the core principle of cryptocurrency, which is self-ownership.
Custodial wallets are common on centralized exchanges where users trade frequently.
Non-Custodial Wallets
Non-custodial wallets give you full control over your private keys. No third party can access or move your funds.
These wallets align with the original idea of decentralization. You own your crypto completely, and no one can restrict your access.
The downside is responsibility. If you lose your private key or recovery phrase, there is no way to recover your wallet. Security practices are entirely up to you.
Non-custodial wallets are preferred by users who value control, privacy, and long-term security.
| Aspect | Custodial Wallets | Non-Custodial Wallets |
|---|---|---|
| Key Control | Exchange/platform holds keys | You hold full control |
| Ease of Use | Beginner-friendly (no seed phrase) | Requires managing seed phrase |
| Recovery | Platform can help (if verified) | Only you can recover (seed phrase) |
| Security | Risk of platform hack/exit scam | Safer from third-party risks |
| Features | Built-in trading, fiat on-ramps | Full DeFi/NFT access |
| Best For | New users, frequent traders | Self-sovereign users, long-term |
| Examples | Exchange wallets (Binance, Coinbase) | MetaMask, Ledger, Trust Wallet |
Common Features of Crypto Wallets
While wallets vary widely, most modern crypto wallets share a core set of features.
They allow users to send and receive cryptocurrency easily using wallet addresses or QR codes. They show balances and transaction history by reading data from the blockchain.
Many wallets support multiple blockchains and tokens. Some include built-in exchange features, allowing users to swap assets directly. Others integrate with decentralized applications for staking, lending, and NFT management.
Security features may include PIN protection, biometric access, encryption, and hardware wallet integration.
Choosing the right wallet depends on how you plan to use crypto, how often you transact, and how much value you intend to store.
Choosing the Right Crypto Wallet
There is no single best crypto wallet for everyone. The right choice depends on how you use cryptocurrency, how often you transact, and how much responsibility you are willing to take for security.
If you trade frequently or use crypto for payments, a hot wallet may be more practical. If you are holding assets for the long term, a cold wallet offers stronger protection. Beginners often start with custodial wallets because they are easy to use, but many move to non-custodial wallets as they gain confidence.
Before choosing a wallet, it is important to consider a few key factors.
First is security. Look for wallets with strong encryption, two-factor authentication, and a clear recovery process. For non-custodial wallets, ensure you understand how seed phrases work and how to store them safely.
Second is supported assets. Not all wallets support every blockchain or token. Make sure the wallet supports the cryptocurrencies you plan to use now and in the future.
Third is ease of use. A clean interface, clear transaction steps, and good documentation matter, especially for beginners. Finally, consider compatibility. Some wallets work only on mobile, others on desktop, and some support hardware wallet integration.
Wondering how cryptocurrency wallets work?
Popular Types of Crypto Wallets in Practice
To understand how wallets are used in real life, it helps to look at common wallet categories and examples.
1. Software Wallets
Software wallets are applications installed on mobile phones or computers. They are usually non-custodial and give users direct control of their private keys.
Mobile wallets are popular for everyday use because they are convenient and easy to access. Desktop wallets are often preferred by users who want more control and are less concerned about mobility.
Many software wallets also support decentralized finance applications, token swaps, and NFTs. This makes them versatile tools beyond simple storage.
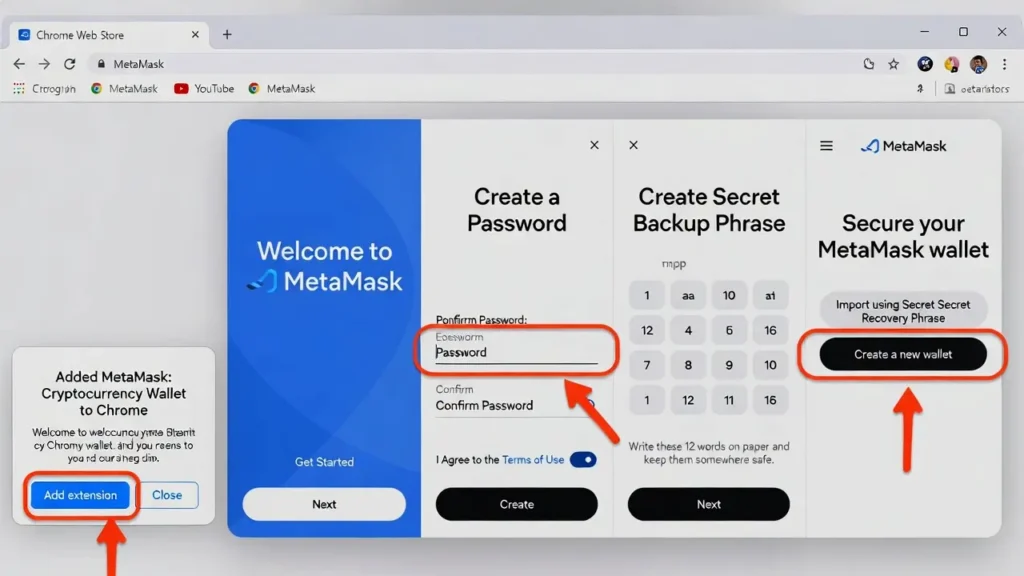
2. Web Wallets
Web wallets run in a browser and are often used to interact with blockchain applications. These wallets are typically hot and non-custodial.
Browser-based wallets are widely used in decentralized finance because they can connect directly to web applications. However, since browsers are common attack targets, users must be careful about phishing sites and malicious extensions.
3. Hardware Wallets

Hardware wallets are physical devices designed specifically to store private keys securely. They are considered one of the safest options for long-term storage. The private keys never leave the device. Even when connected to a computer, transactions are signed internally. This significantly reduces the risk of theft through malware.
Hardware wallets are best suited for users holding large amounts of crypto or those who prioritize security over convenience.
4. Exchange Wallets
Exchange wallets are custodial wallets provided by centralized platforms. They are commonly used for trading and short-term holding. These wallets simplify buying and selling crypto, but they require trust in the exchange. History has shown that crypto exchanges can be hacked or mismanaged.
A common recommendation is to avoid storing large amounts of crypto on exchanges for long periods.
| Type | Description | Best For | Popular Examples (2026) | Pros | Cons |
|---|---|---|---|---|---|
| Software/Mobile | App on phone/computer | Everyday use | Trust Wallet, Exodus, MetaMask | Free, easy, multi-chain | Online risk |
| Web/Extension | Browser-based | DeFi/NFTs | MetaMask, Coinbase Wallet | Quick dApp access | Phishing vulnerable |
| Hardware | Physical device | Secure long-term storage | Ledger Nano X/S, Trezor Model T | Offline keys | Cost, less convenient |
| Exchange | Built into trading platform | Beginners/trading | Binance, Coinbase, Kraken | Integrated trading | Not your keys |
Read our guide How to Check If a Crypto Exchange Is Safe: A Complete Security Checklist
Wallet Security Best Practices

Security is the most important aspect of using a crypto wallet. Even the best crypto wallet can fail if used carelessly.
Always back up your recovery phrase and store it offline. Never store it in cloud storage, email, or screenshots. Writing it on paper or using a metal backup is safer.
Never share your private key or seed phrase with anyone. No legitimate service will ever ask for it.
Be cautious of phishing attacks. Always double-check website URLs and avoid clicking unknown links. Many scams look professional and convincing.
Keep your devices updated. Security updates reduce vulnerabilities that attackers can exploit.
If possible, use a hardware wallet for long-term storage and keep only small amounts in hot wallets for daily use.
| Feature | Why It Matters | Common In | Recommendation |
|---|---|---|---|
| Seed Phrase Backup | Recovery if device lost | All non-custodial | Store offline, never share |
| 2FA / Biometrics | Extra login protection | Most software/web | Use app-based, not SMS |
| Address Whitelisting | Limits withdrawals to approved addresses | Many exchanges/hardware | Enable for large holdings |
| Multi-Sig Support | Requires multiple approvals | Advanced wallets | For teams/high-value |
| Open-Source Code | Community-audited security | Trezor, some software | Prefer for transparency |
Common Wallet Mistakes to Avoid
Many beginners lose funds due to simple mistakes rather than technical failures.
One common mistake is assuming the wallet stores the coins. This leads to poor backup habits. Remember that the wallet stores keys, not assets.
Another mistake is relying entirely on custodial wallets without understanding the risks. Convenience should not replace awareness.
Sending crypto to the wrong address or wrong network is another frequent error. Blockchain transactions are irreversible. Always double-check addresses and networks before confirming.
Finally, neglecting education is a mistake. Crypto wallets are powerful tools, but they require a basic understanding to use safely.
The Role of Wallets in the Crypto Ecosystem
Crypto wallets are more than storage tools. They are gateways to the broader blockchain ecosystem. Through wallets, users can access decentralized finance platforms, participate in governance, stake tokens, mint NFTs, and interact with smart contracts.
As blockchain technology evolves, wallets are becoming more advanced. Many now include portfolio tracking, fiat on ramps, and multi-chain support.
Despite these advancements, the core purpose remains the same. A wallet exists to give users control over their digital assets.
Final Thoughts
A crypto wallet is the foundation of cryptocurrency ownership. It defines how you store, use, and protect your digital assets. Understanding the differences between hot and cold wallets, as well as custodial and non-custodial options, helps you make informed decisions. There is no perfect wallet, only the one that fits your needs and risk tolerance.
For beginners, starting simple is fine. As your knowledge grows, moving toward greater control and stronger security becomes important.
Crypto rewards those who take responsibility seriously. A well-chosen wallet, used correctly, is not just a tool. It is your personal vault in the digital economy.
With the right approach, a crypto wallet becomes less intimidating and more empowering. It turns blockchain from a concept into something you can actually use with confidence.
FAQ
Do crypto wallets actually store my Bitcoin or Ethereum?
No – they don’t hold the coins themselves. Your crypto stays on the blockchain forever. The wallet just stores the keys that let you access and move it.
What’s the difference between a hot wallet and a cold wallet?
Hot wallets are connected to the internet (like phone apps or browser extensions) – super convenient for trading but riskier if your device gets hacked. Cold wallets stay offline (hardware like Ledger or even paper backups) – way safer for holding large amounts long-term.
Is it safe to keep my crypto on an exchange wallet?
It’s okay for small amounts or quick trading, but remember: “not your keys, not your crypto.” Exchanges can get hacked or freeze accounts. For serious holdings, move to your own non-custodial wallet.
What happens if I lose my seed phrase?
You’re probably locked out forever – no seed phrase means no recovery. That’s why you store it offline in multiple safe places (never digitally). Treat it like the keys to your house.
Should beginners start with MetaMask or a hardware wallet?
Start with something simple like MetaMask (free browser extension) to learn the ropes – it’s great for Ethereum stuff. Once you have more crypto, get a hardware wallet like Ledger for real security.
How do I know if my wallet is secure?
Look for features like 2FA, seed phrase backups, and no unnecessary permissions. Stick to official downloads, never share your seed phrase, and enable address whitelisting if available.
Can one wallet hold all my different cryptos?
Most modern ones (Trust Wallet, Exodus, Ledger) support hundreds or thousands of coins across chains. Just check compatibility before transferring.
What’s a seed phrase and why is it so important?
It’s a 12-24 word backup code generated when you create a wallet. Anyone with it can access your funds, so keep it secret and offline. It’s your ultimate recovery tool if your phone dies or device breaks.